Module_11: Network Sniffing and Man-in-the-Middle (MITM) Attack
Module_11: Network Sniffing and Man-in-the-Middle (MITM) Attack
About Course
Learning Objectives
By the end of this module, learners will be able to:
-
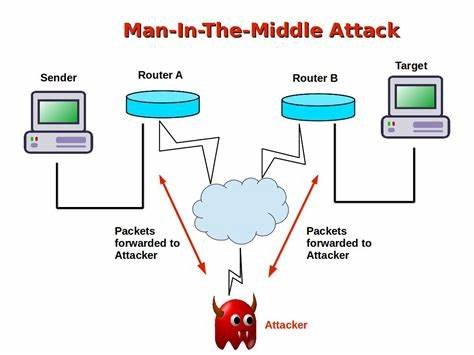
Understand the concepts of network sniffing and Man-in-the-Middle (MITM) attacks.
-
Learn how attackers intercept and manipulate network traffic during MITM attacks.
-
Explore tools such as Mitmproxy for performing traffic interception and analysis.
-
Perform step-by-step simulations of MITM attacks in controlled environments.
-
Analyze real-world scenarios of MITM attacks in institutional or organizational networks.
Learning Outcomes
After completing this module, learners will be able to:
-
Explain how network sniffing and MITM attacks compromise data confidentiality and integrity.
-
Demonstrate the ability to capture and analyze network traffic using appropriate tools.
-
Execute MITM attack simulations using Mitmproxy in a safe lab setup.
-
Identify vulnerabilities that allow traffic interception in networks.
-
Recommend and apply security measures to prevent MITM attacks in real-world environments.
Total Duration for module Completion: 5 Hours
Course Content
Pre session Quiz
-
Quiz
11.1 Course Overview
11.2 Man-in-the-Middle (MITM) attack using Mitmproxy
11.3 Activity MITM Attack demo on Education institute
Post session Quiz
Student Ratings & Reviews

No Review Yet
